Hacktivate: Empowering the Next Generation of Ethical Hackers
Paul Hudson introduces Hacktivate, an app empowering kids (13+) to learn ethical hacking. Through engaging 'capture the flag' challenges, it teaches SQL injection, steganography, and core cybersecurity skills in a safe, interactive environment.

Why I’m Teaching Kids to Hack Computers
By Paul Hudson, @twostraws, October 22nd 2025
When I was a teenager, my understanding of computers grew from a cycle of experimentation: trying things, breaking them, and then fixing them again. This relentless curiosity, coupled with the more open nature of computers at the time, allowed me to learn and develop profoundly.
Today, computers are significantly more polished and secure, which is understandable. Most users aren't interested in the command line, don't care about binary code, and are often unaware of concepts like packet sniffing.
However, I'm passionate about recreating those formative experiences for a new generation. To achieve this, I developed a comprehensive "capture the flag" game designed to teach kids aged 13 and older practical skills such as SQL injection, using rainbow tables for hash cracking, employing steganography to hide data in images, and much more.
My objective was to blend a touch of the dramatic flair often seen in movies – reminiscent of games I loved like Syndicate, Command & Conquer, and Uplink – with real-world skills in networking, cryptography, digital forensics, and other areas. The aim was to create an engaging platform that teaches fundamental computer science concepts in an enjoyable way.
I want to share my goals for building the app, the challenges I encountered, the technologies utilized, and more. I hope you find this insight valuable!
If you prefer to jump straight into the experience, you can try the app yourself by clicking here.

What’s the Problem?
While there's no shortage of "learn to hack" resources available, many suffer from one or more common issues:
- Dry and Academic: They often focus on theoretical reading and question-answering.
- Limited Access: Availability might be restricted to specific groups or times, such as national cybersecurity competitions.
- Lack of Guidance: Challenges can be interesting but offer no clear path to solving them.
- Shared Resources: The use of shared environments often prevents users from performing actions like rewriting database entries or deleting files.
Some of these limitations are unavoidable; pursuing a serious career in cybersecurity does necessitate a deep dive into theoretical study. However, collectively, these issues can create a discouraging environment. Students want to engage with real tools and technologies, but they also seek a clear, guided path forward, and crucially, they want the learning process to feel exciting, especially when they are just starting out.
This is the gap I aimed to fill: to create a structured experience with scaffolded challenges that feel cinematic while imparting practical skills.
The result is Hacktivate, now live and available on iPhone, iPad, and Mac. It comes in two editions:
- One-time upfront payment, with no in-app purchases.
- Free to play, with in-app purchases for game content and hints.
Both versions offer the same challenges and functionality.
Building a Safe Place to Break Things
I embarked on building a solution that addresses these problems by:
- Providing 240 "capture the flag" challenges covering topics such as SQL injection, the Linux command line, JavaScript, hashing, encryption, and more.
- Teaching students the essential computing, security, and logic skills required to solve these challenges.
- Utilizing safe sandboxing, ensuring that all data, servers, and hacks are performed within the game environment, without affecting real-world targets.
My primary goal is not to instantly transform everyone into a seasoned penetration tester, but rather to inspire a new generation of aspiring hackers to experiment, learn, and enjoy themselves in a secure and structured manner.
As you might expect, this undertaking required a significant amount of effort.
Part of this work involved developing tools to simulate real-world data within a self-contained app. Features like packet sniffing, network routing, and DNS lookups all had to function without the user needing to leave the app, even when offline. (I even cached DNS results for the servers used in challenges!)
However, the most substantial portion of the work was dedicated to meticulously crafting all the challenges. Unlike a platform game where a core engine can be reused across different levels, cybersecurity challenges cannot simply repeat; each one needs to be more or less unique to remain engaging.
For example, one challenge might require discovering that a single PNG file actually contains multiple images, another might involve deciphering a message spelled out using mixed decimal, hexadecimal, and octal ASCII values, while another hides a flag within a regex crossword. Yet another challenges players to log into a virtual email inbox to find the next target of a cybercriminal organization.

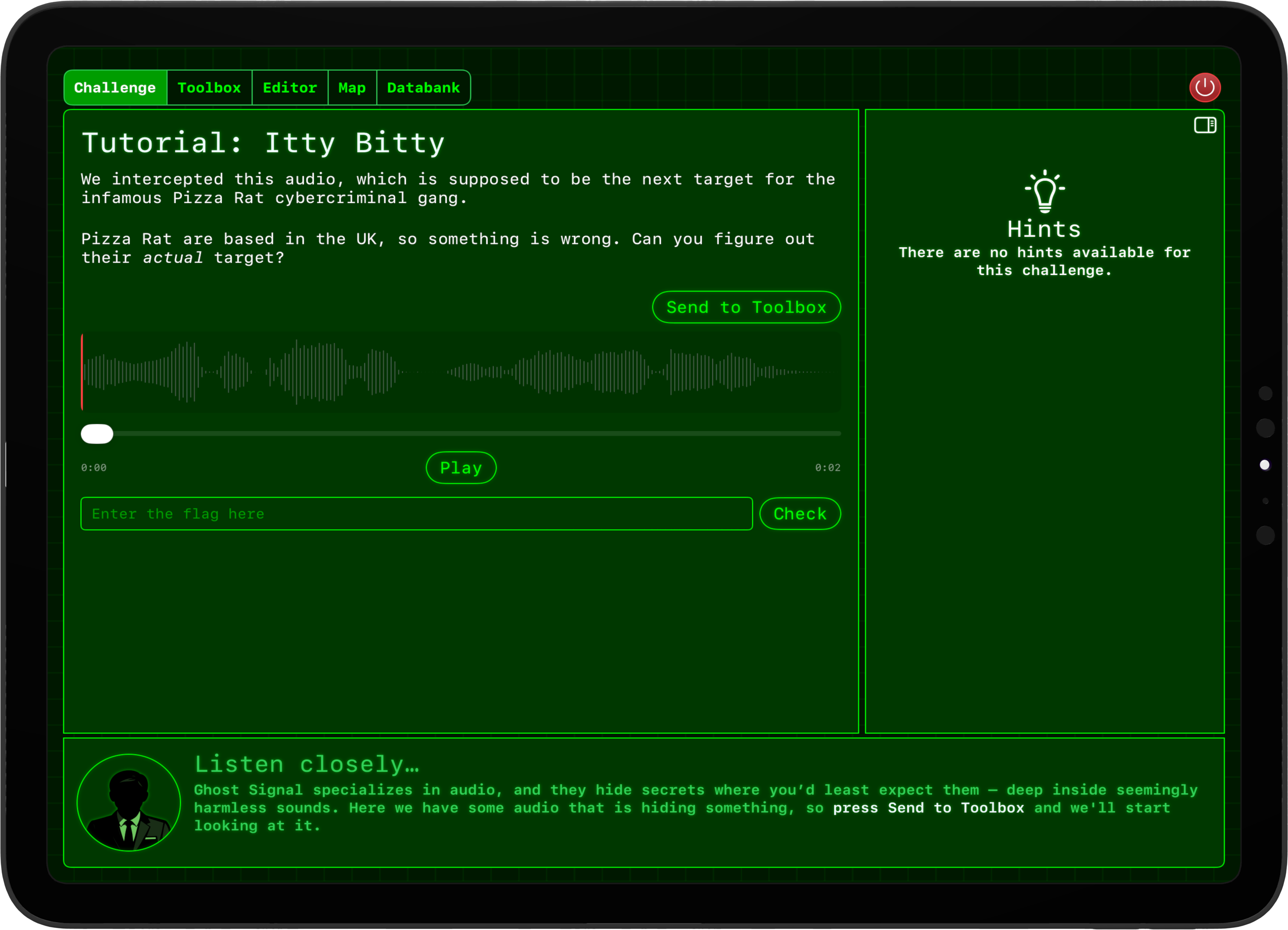
What Hacking Looks Like Inside Hacktivate
The game features a diverse array of challenges. I’d like to highlight a few and discuss their implementation:
- Basic data-handling questions: These cover hex, binary, ASCII, Base64, and similar formats. They teach students about data representation and were relatively straightforward to create, primarily focusing on recognition skills.
- Cryptography challenges: Starting with classic codes and ciphers (Caesar, Vigenère, Morse), these progress to modern hashing and encryption methods like SHA1/2/3, Enigma, and AES. These became increasingly difficult to design, as the aim was to provide just enough information for students to solve them independently, without revealing too much.
- Browser-based challenges: All these run locally on the user’s device. They begin with trivial tasks (e.g., passwords hidden in HTML comments), advance through concepts like HTTP headers and cookies, and then move on to more complex vulnerabilities such as IDOR (Insecure Direct Object References) and SQL injection. These were surprisingly easy to create, largely due to the vast number of web-based vulnerabilities available 🫠 Internally, the app runs a private web server, allowing dynamic adjustment of page content as players advance through challenges.
- Terminal-based challenges: These also run entirely on the user’s device. This set was the most challenging to develop, primarily due to the requirements of shipping the app on Apple’s platforms. I ended up building a full Linux terminal emulator, complete with various core commands (e.g.,
ps,cat,netstat,nc,strings,sudo). This enabled the creation of challenges involving rogue servers, suspicious commands in user history, and files owned by different users. - Networking challenges: Starting simply (e.g., finding the optimal route from A to B, identifying the flag within a list of IP addresses), these escalate in difficulty to include concepts like packet sniffing and ARP spoofing.
- Steganography challenges: Distinct from regular cryptography, these also progress from simple tasks (“if you reverse the audio and speed it up you can hear a voice!”) to more complex scenarios like “if you read the least significant bits of this audio file and treat them all as grayscale image data, you get the flag.”
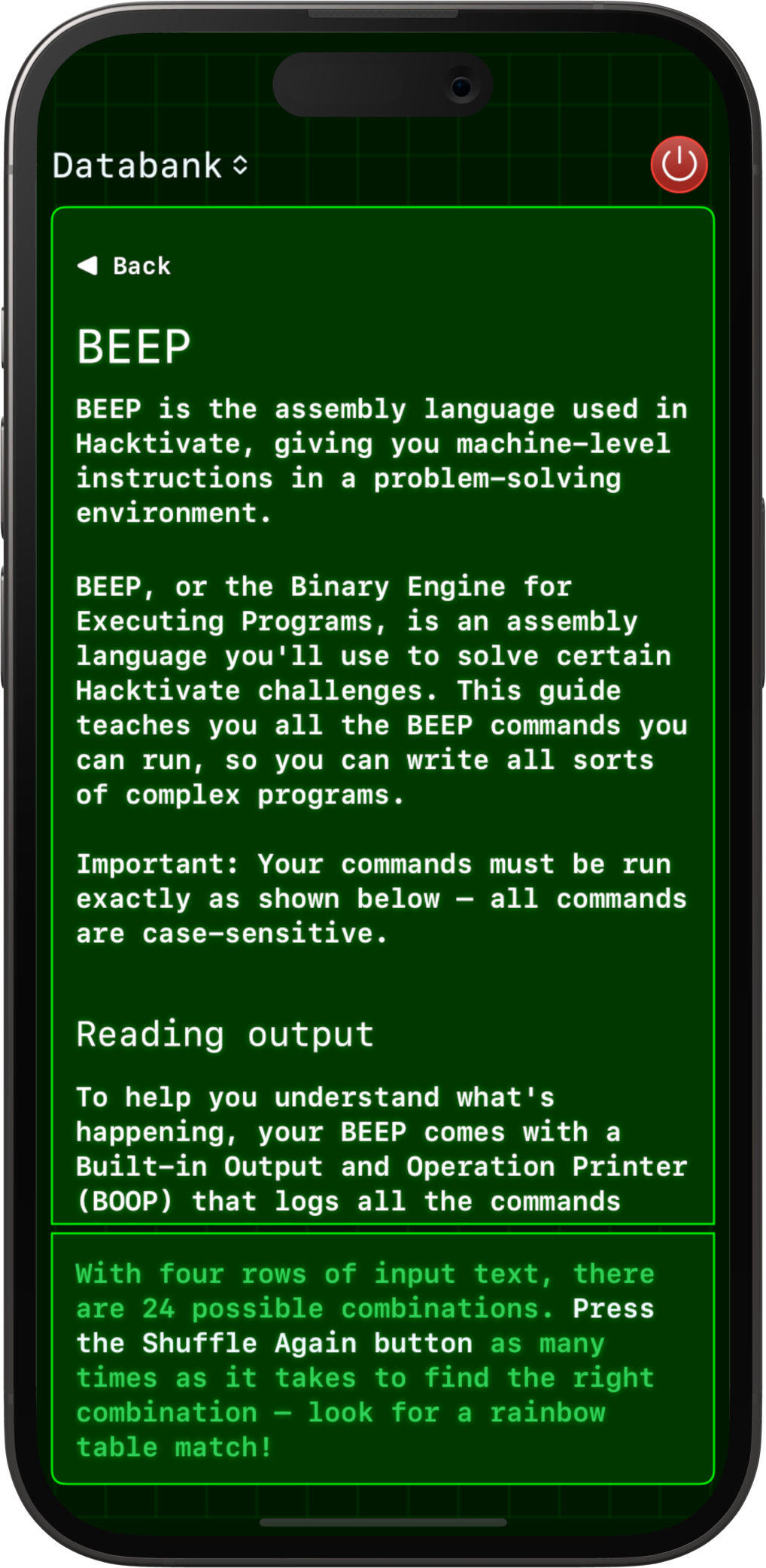
And these are just a few examples. Students delve into regex crosswords, substitution ciphers, robots.txt, Unicode, OSINT, logic gates, and much more. There’s even an entire virtual assembly language used in some challenges!
A key advantage of the app running on a local device is complete privacy: there are no trackers, analytics, advertisements, cookies, or similar data collection. Everything you do remains private to you.
Note: A separate version of Hacktivate, called Hacktivate: Education Edition, removes all in-app purchases, relying instead on a single, upfront payment. If you dislike micro-transactions (understandable!) or if you work in schools where in-app purchases are not feasible, this edition is the recommended download.

Under the Hood
The entire application is written in Swift and SwiftUI, enabling compatibility across iPhone, iPad, and Mac. While I anticipate some eye-rolls from certain audiences, Apple has been incredibly supportive throughout the development process, offering extensive help and guidance to optimize the app, including code-level assistance for issues.
(For those firmly against Apple devices, there’s also a web version of Hacktivate – it's not as powerful or engaging, but it's entirely web-based and free!)
Artificial intelligence played a role in the app's creation, primarily within its “toolbox”—my custom version of CyberChef, where users can build recipes to transform data in various ways to uncover flags.
Some of the tools in this toolbox were highly complex to implement, and AI proved invaluable here. For instance, the Enigma machine implementation, parsing SSH host keys, the SHA family of hashes, and audio transformations were almost entirely generated by AI. These are intricate, precise algorithms, and with careful prompting, Claude performed exceptionally well in implementing them correctly.
However, the vast majority of the app was written manually by me, as AI currently struggles with true originality. I sought challenges that felt crafted and intentional, allowing users to feel a clear progression in their skills, rather than simply presenting hundreds of random AI-generated ideas.
As of today, the final tally stands at 45,132 lines of Swift code, 164,680 lines of JSON, plus additional HTML, CSS, and Markdown. The JSON not only contains challenge information but also all the simulated data—such as virtual email inboxes, terminal configurations, packet captures, and even an entire social network used in one specific challenge.
Beyond my own work, I collaborated with several designers from Fiverr for elements like team and player icons, integrated open-source libraries such as SQift for local SQL database manipulation, and utilized Creative Commons media from artists like Brad Sucks to provide interesting content for hiding flags.
I also created a YouTube video walking through various parts of the Hacktivate code.
Influences from Old-School Games
Despite being powered by real-world skills, I wanted Hacktivate to capture a touch of the “Hollywood hacker” aesthetic—to feel both retro and cool, enhancing the fun factor for students.
I drew significant inspiration from three beloved games:
- The core of the UI was heavily influenced by Bullfrog Productions’ game, Syndicate. The green-screen interface, screens drawing themselves with a laser effect, and the squared-off map with icons were among the first elements I built. I knew I wouldn't continue development unless I genuinely found this aspect enjoyable.
- Other UI components, particularly text rendering and animations, were inspired by Westwood Studios’ Command & Conquer.
- Finally, Introversion Software’s game, Uplink, provided numerous ideas, although our approach differs significantly. Uplink leans heavily into the Hollywood hacker trope, whereas Hacktivate strives to remain anchored in genuine skills.
I believe the outcome is successful: the interface feels suitably fun and retro, with a light sprinkling of animations, particle effects, and haptics adding small moments of surprise and delight, while still managing to integrate all the powerful tools necessary to solve the challenges.
Here’s a video of the C&C installer from their remastered edition—I think the parallels are quite clear!
Where it Goes Next
My ultimate goal is certainly not to create a horde of black hat hackers. Instead, I aim to create something enjoyable and engaging that provides students with safe learning opportunities. I also hope to inspire new individuals to consider cybersecurity as a career; with recent high-profile attacks on companies like Jaguar Land Rover, Asahi, and F5, demand has never been higher.
Even if students primarily use it for fun, I hope it at least equips them to better spot scams, secure their own data, and thoughtfully consider online privacy.
There’s still plenty of room for improvement within the app:
- Improving screen reader support is my top priority right now, ensuring the game is as accessible as possible.
- I’m contemplating adding a leaderboard system, though I want to ensure it’s implemented in a privacy-preserving way, consistent with the rest of the app.
- I’d like to add support for achievements, badges, and similar rewards as users complete challenges. Apple’s Game Center offers a fun way to integrate this.
- I will also continue refining the iPhone UI. The app is packed with functionality, and adapting that to a phone-sized screen was a considerable challenge.


Want to Try It?
If you enjoy puzzles, packet captures, or following obscure digital breadcrumbs, Hacktivate is available now on the App Store.
You can try 10 tutorial challenges for free, and unlock 240 more with a one-time purchase.
When you purchase the unlock, it works across all your Apple devices, with your progress automatically synced between them.
I’d love to hear your thoughts, or what kinds of challenges you’d like to see next!

About Paul Hudson
Paul Hudson is the founder of Hacking with Swift, the world’s largest website dedicated to building apps for Apple’s platforms.
Paul has been developing apps for iPhone since 2009, during which he has collaborated with teams at Apple, Autodesk, UBS, Xerox, and various other organizations.
Paul resides in Bath, England, with his two daughters and two dogs.
Contact Details
Email: paul@hackingwithswift.com Twitter: @twostraws Mastodon: @twostraws GitHub: @twostraws
Email Me
