Secure Password Storage in Databases: A Simple Guide
Learn essential techniques for securely storing user passwords in your database. This guide covers modern hashing algorithms like bcrypt and the importance of salting to prevent common attack methods.
Safeguarding user passwords is paramount. Even if your database is compromised, proper storage techniques must prevent attackers from accessing plaintext passwords. Never store passwords in plaintext.
OWASP Recommendations for Secure Password Storage
The Open Web Application Security Project (OWASP) outlines two critical components for secure password storage:
1. Employ a Modern Hashing Algorithm
A hash function performs a one-way mathematical operation. You can transform a password into a hash, but you cannot revert a hash back to the original password.

However, not all hashing functions offer the same level of security. Common algorithms like MD5 and SHA-1 are fast, which, counterintuitively, makes them unsuitable for passwords. Their speed allows attackers to perform billions of password guesses per second via brute-force attacks.
Instead, you should use password-specific hashing algorithms designed to be intentionally slow and resource-intensive, such as bcrypt. These specialized algorithms significantly increase the computational cost and time required for brute-force attacks, making them impractical for malicious actors.
2. Salt the Passwords
A salt is a unique, randomly generated string that is added to each password before it is hashed. This ensures that even if two users choose the same password (e.g., "password123"), their resulting hashes will be entirely different.
Why is salting crucial?
Without unique salts, attackers can employ precomputed attack methods:
- Rainbow Tables: These are vast databases containing precomputed hashes for countless common passwords. If a hash in your compromised database matches one in a rainbow table, the password is instantly revealed.
- Database Lookups: Attackers can quickly search for matching hashes within their own databases of compromised credentials, cracking passwords in mere seconds.
By incorporating a unique salt into each password before hashing, you guarantee that every generated hash is distinct. This renders precomputed attacks, such as rainbow tables and simple database lookups, completely ineffective.
How It Works: User Registration Flow
When a new user creates an account, the process for secure password storage unfolds as follows:
- The user submits their chosen password.
- The system generates a unique, random salt (e.g.,
k8Px2mN9). - The system combines the user's password with this newly generated salt.
- A strong hashing algorithm, such as bcrypt, computes a hash from the combined password and salt.
- Finally, the system stores both the resulting hash and the salt in the database.
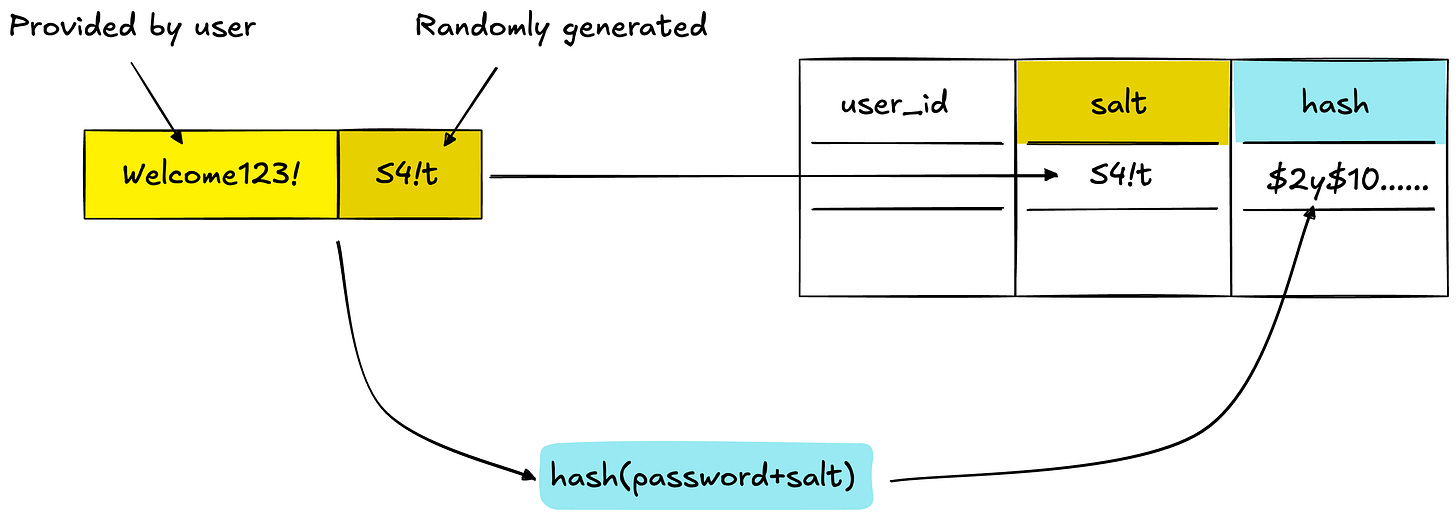
It's important to note that the salt itself is not a secret. It can be stored in plaintext alongside the hash in the database. Its primary function is to ensure the uniqueness of each hash, not to conceal information.
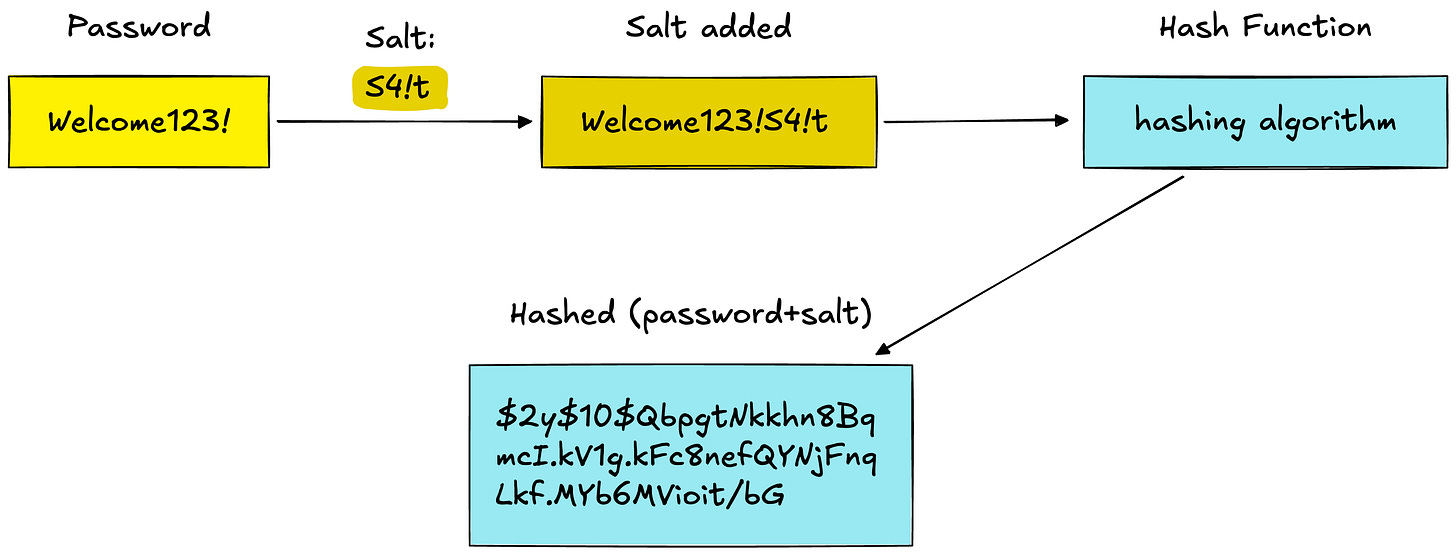
Example:
- Password: "Welcome123!"
- Salt: "S4!t"
- Combined: "Welcome123!S4!t"
- Hash:
$2y$10$Qbpn8Bq...b6MVioit/bG(This is the value stored in the database.)
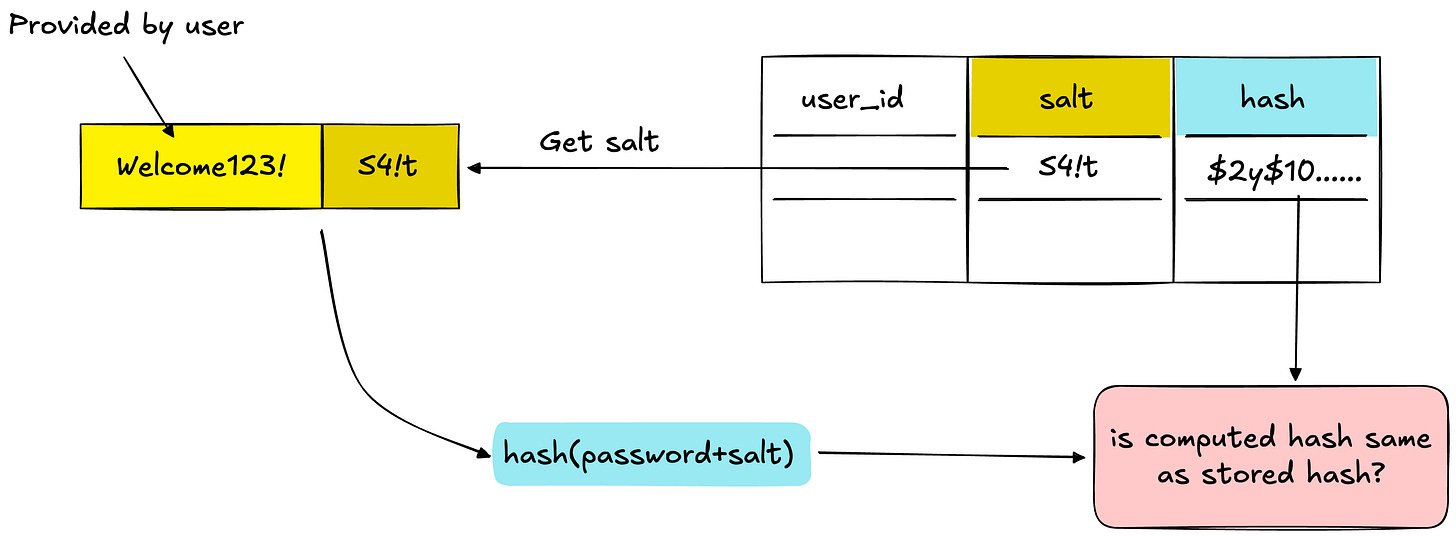
How It Works: Login Validation
When an existing user attempts to log in, the system validates their credentials as follows:
- The user submits their username and password.
- The system retrieves the user's stored hash and associated salt from the database.
- The system appends the retrieved salt to the submitted password.
- A new hash is computed from this combined string using the same hashing algorithm (e.g., bcrypt).
- The newly computed hash is then compared against the hash stored in the database. If they match, the password is valid, and authentication is successful. ✓
Additional Security Layers
Beyond hashing and salting, consider implementing these complementary security measures to further bolster user account protection:
- Rate Limiting: Restrict the number of login attempts allowed from a specific IP address or for a particular user account within a given timeframe.
- Account Lockout: Temporarily disable user accounts after a predefined number of consecutive failed login attempts to thwart brute-force attacks.
- Adaptive Hash Parameters: Periodically increase the "cost factor" (or work factor) for algorithms like bcrypt. As computing power advances, increasing this parameter ensures the hashing process remains computationally expensive for attackers.
- Pepper (Optional): Introduce a secret key, known as a 'pepper', which is concatenated with the password and salt before hashing. Crucially, the pepper must be stored outside the main database (e.g., in an environment variable or separate secrets management system) to provide an additional layer of defense against database compromises.